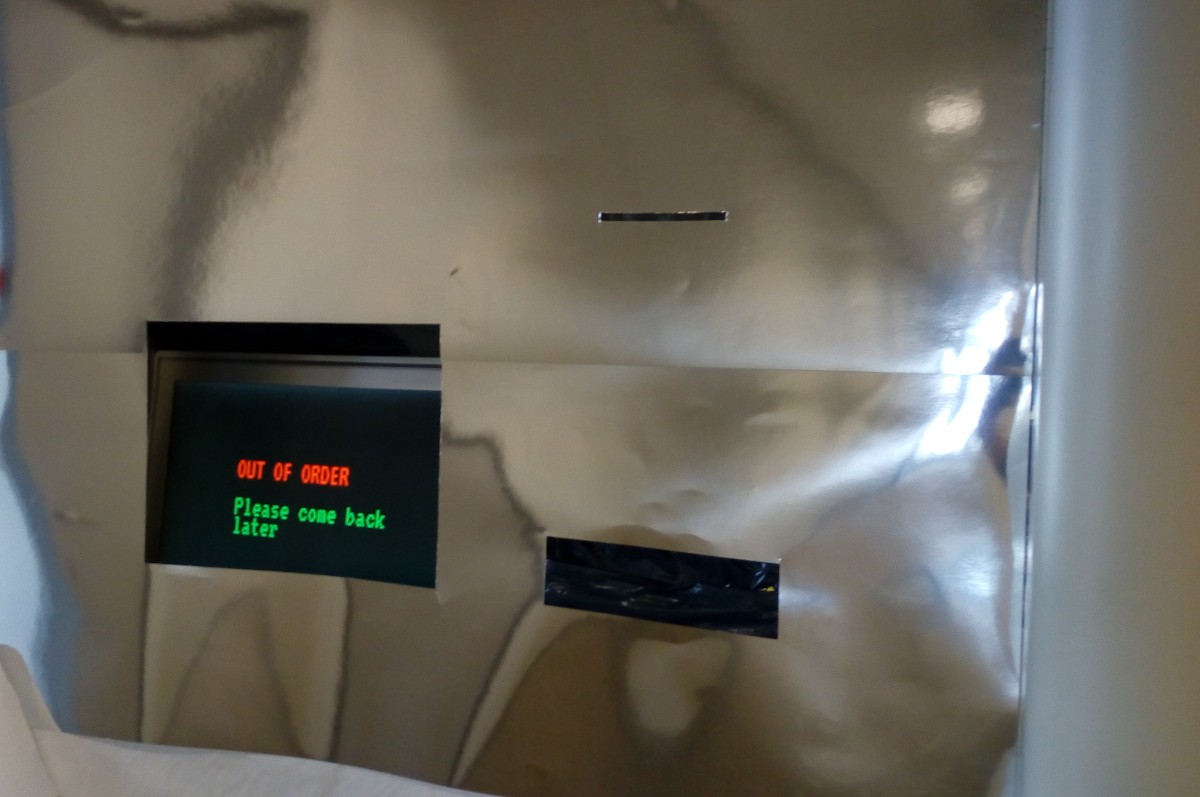
Interactive installation developed and presented at the Techno-Galactic Software Observatory.
How: Visit the Future Blobservation Booth to have your fortunes read and
derive life insight from the wisdom of software.
What: Put your hand in the reading booth and get your line read.
Why: The hand which holds your mouse everyday hides many secrets.
-
Electromagnetic radiation gives information on your battery.
Using devices is a liability. Cliché, yes, but the contemporary human needs an acute awareness of their own vulnerabilities. Remember that eavesdroppers will be able to employ advanced techniques to glean precious information such as your laptop's battery level.
-
Beware the app rhetoric.
In a world of apps and services, one needs to be wary of an over-reliance on software to cure their maladies. This includes your career choices and employment status. If you feel desperate, consider turning yourself off and on again.
-
Software time is not the same as human time.
Computers will run for as long as they will be able to, provided sufficient power is available. You, as a human, don't have the luxury of being always connected to the power grid and thus have to rely on your internal battery. Be aware of your power cycles and set yourself to power-saving mode whenever possible.
-
Visualizing your productivity can help.
Computers schedule their processes and priorities; you should too. Do a post-mortem analysis of the last time you used your digital device: what did you do? How long did your tasks take? Did you find yourself spending more time than you initially planned? Open your consciousness to the ways software shapes your actions; writing it down as an exercise is a great start.
-
Probe your work ethic through side-channel analysis.
Side-channel analysis means analysing software by looking at the hardware. In the same vein, it's a useful exercise to understand your own mind rhythm by focusing on your body's state. For instance, not drinking enough water will make you tired and grumpy. Perhaps it's not your mind, but your body that is the source of the bug.
-
Observe your hardware as well as your software.
Computing is made out of both. Cliché, yes, but contemporary discourse tends to focus on the software and not so much on the physical medium that supports it. What is that computer doing in your pocket? Remember when there was a dedicated place in your home for computing? What happened since then? Hard questions often imply uncomfortable answers. Don't shy away from looking for them nevertheless.
-
Screens can be an attack vector.
The screen looks like a neutral element in your relationship with computers, but is it really? Did you know that blue light emitted from screens interferes with your sleep patterns? Have you thought that the person behind you on the subway can perfectly read the message your lover has sent you just now? Raise your screen with the same awareness that you would open your wallet in public.
-
Optimize for the layout of your processor.
It is tempting to try and support all possible architectures, but this can ultimately lead to frustration and incomplete endeavours. Consider your own personal architecture and design your own mind software for it; then, and only then, should you consider porting your own personal code to other systems.
-
Computing is where things start and where things end.
In more ways than one, us humans rely on simple processes to function and exist. Whether it's writing a text file, reading a web page or editing a video, the underlying operations are the same. Have you thought of the building blocks of who you are and what you do? Focusing on the elementary code of your being can be surprisingly liberating, even if not immediately intuitive. Just start thinking about it and see where it leads you.
-
Use antennas to understand the signals you're emitting.
Antennas are ultimately rudimentary devices: rods, strands of metal or cans of potato chips. Nevertheless, they're a crucial ingredient of the most complex network layouts. How can you try and read your own procedures through elementary means? Perhaps the answer is much closer than you think.
-
Attacking your system is the best way to find your own weaknesses.
Security conscious enterprises are eager to find the best hackers to test the security of their own systems. Imagine yourself trying to break into your system. Where are the dents in your walls? Is there any hole you might be unaware of? By staging an "attack" on your own self you might be able to derive insights on your own vulnerabilities.
-
Don't raise your volume control to excessive levels.
If you're listening to your favourite song, it is tempting to raise the volume while ignoring your phone's warnings that it might damage your ears. Do you see any parallel between this and your daily existence? In which cases are you cranking up the sound? Which warnings are you ignoring? And what kind of damage might you be incurring? The fact that some questions are hard to face shouldn't deter you from finding the inevitably uncomfortable answers.
-
Consider the link between the entrepreneurial environment and precarious practices when designing your own software.
The Entrepreneur effect suggests that, once we start designing software, we will unconsciously ignore certain dilemmas and hard questions. This is a natural process with the goal to avoid reflecting in the precariousness of the environment that we are working on. Taking time to secure and root your practice is more important than engaging in dangerous confrontations.
-
If we use, we know.
Empowerment comes through experience. Forfeit the administrator role: distance yourself from your deeply-rooted beliefs and become a user of your own system. Read your own manual pages and find out better ways to run your own commands. Look it up online if you are lost, but avoid suffocating your inevitable thirst for knowledge. Immerse yourself through use and when the time is right, knowledge will come to you.
-
Bad people will want to steal your battery.
Resources such as battery power or a constant internet connection are valuable to-haves. Isn't it wonderful to be connected all the time? To have five bars of connectivity or 100% battery? These are precious luxuries that will be constantly put in check by outside agents. Beware of external elements that disturb your connectivity, destabilize your emotions and which perform attacks on your server in order to bring it down.
-
You're under constant attack: employ mitigation tactics.
You can't stop every single negative input, every single malicious connection to your service. What you can do, however, is to make it harder for those to reach your core. Build up your firewall and detect the IP addresses that are coming back to harm you so that you can effectively ban them. Face life with the mindset of mitigation: you cannot stop the attacks from coming, but you can and should minimize the damage caused.
-
Computers work the same during work-hours and off-hours. Be a computer.
While your work-life and daily life are naturally separate, there are aspects of existence that will require the same level of vigilance. Your firewall can't become weaker outside certain time slots, don't you agree? Computers have specific software to be vigilant and ensure that all defenses are up and running. Install that kind of software in your own self and ensure your defenses are always online.
-
Break the cypher of your obstacles.
Even in the most secure systems where the key is hidden behind many layers of obfuscation, there always is a way in. Even if the gates seem unsurmountable, it is most often a matter of realising the pathway, which usually requires you to think outside the box. Exit the box of your own thought restrictions, and visualize the route to gain access to the cypher that will allow you to crack your problems.
 Manufactura Independente
Manufactura Independente